NDAA and Cybersecurity Continue Relation in 2013 in New Provision

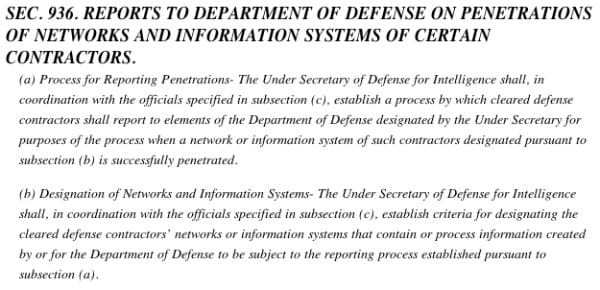
It’s no hidden truth that cybersecurity is becoming an increasingly important issue for the U.S. government to address. It is listed as a top issue concerning the Department of Defense, with extensive resources dedicated to cyber-defense. On Thursday, Armed Services Committee Chairman Carl Levin (D-MI) addressed the Senate floor revealing the most recent conference report, which is approving significant increases in funding for the Pentagon’s cybersecurity endeavors. NDAA for the 2013 fiscal year also includes a new provision sponsored by the Senator, Section 936, which will implement an extensive cybersecurity reporting process for private defense contractors.
In his address to the floor, Levin said of the newest NDAA and cybersecurity:
"The conference report requires the Secretary of Defense to create a process requiring defense contractors that use or possess classified or sensitive DOD information to report successful cyber penetrations of their networks or information systems. Additionally, if the Department is concerned about a particular event and feels the need to determine what DOD information may have been lost, the provision would authorize DOD to conduct its own forensic analysis, upon request, and subject to limitations. This represents a major breakthrough in the Nation’s cybersecurity. However, other sensitive areas where we are threatened with cyber attacks, such as the financial, police and transportation sectors, need similar action."
The initiative was met with resistance from the tech industry, many companies of which believe the new requirements will be too costly and could detract money from other important cybersecurity programs and research. The intense backlash was addressed by amending some of the section’s language, prompting some flexibility from the private contractors. However, they make clear that their official position on the requirements can only be determined once the Pentagon actually writes the specific rules for reporting implementation and develop baseline software assurance standards.
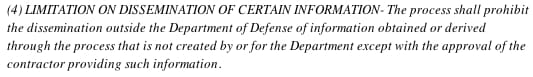
Previous to Thursday’s statement, little had been said of the NDAA and cybersecurity, in particular Section 936's sneaky appearance. (Although, it is noteworthy to mention this isn't its first appearance. NDAA of 2012 allotted generous funds to the Dept. of Defense's Cyber Command and other research and development programs). The details of Sec. 936, now enumerated 941, popped up on several law blogs in the first half of December, however. A blog called Lawfare, expressed concern about the provision’s meaning. The author of the post, Mr. Paul Rosenzweig, who heads homeland security consulting company Red Branch Consulting, wrote of Section 936:
Almost seems the worst of both worlds — mandatory disclosure without any liability protection for the contractors AND no comprehensive improvement in information sharing about threats and vulnerabilities by keeping the information stove-piped. Sec. 936,d,4
A previous House initiative sponsored by Rep. Mac Thomberry (R-TX) additionally attempted to detail the Pentagon's distinct role and power in cyberspace in the NDAA, but this was met with resistance and the White House had promised to veto such a bill. Such detail has been removed from the bill.
Essentially, the government is hanging in an interesting limbo regarding cybersecurity; they try navigating protecting against increased threats of security breaches by hackers via cyberspace, addressing concerns of classified information leaks, while maintaining an important sense of freedom, independence, and discretion online. The result of Sec. 936 (941) remains to be seen, both in its efficacy in curbing hackers' activities within classified realms and in its procurement of further government control on cyber-processes.